Security and cybersecurity are of the upmost important for all of us. Scam emails are unfortunately received very often. Below are some measures you can take if you receive such emails.

Phishing
Cybercriminals are updating their skills but phishing remains one of the most popular form of cyber-crime used to scam individuals and steal financial and personal information. Our best defense is to stay vigilant and informed by familiarizing ourselves with the best practices.
Unmasking the many faces of phishing

Phishing
Typically, you receive an email that appears to come from a reputable organization such as a bank. The email includes what appears to be a link to the organization’s website. However, if you follow the link, you are connected to a replica of the website. Any details you enter, such as account numbers, PINs or passwords can be stolen and used by the hackers.

Spear phishing
Unlike phishing which involves mass-emailing, spear phishing is small-scale and well-targeted. The hacker emails users in a single business. The emails may appear to come from another staff member at the same company and ask you to confirm a username and password. A common tactic is to pretend to be from a trusted department that might plausibly need such details, such as IT or Human Resources. Sometimes you are redirected to a bogus version of the company website.

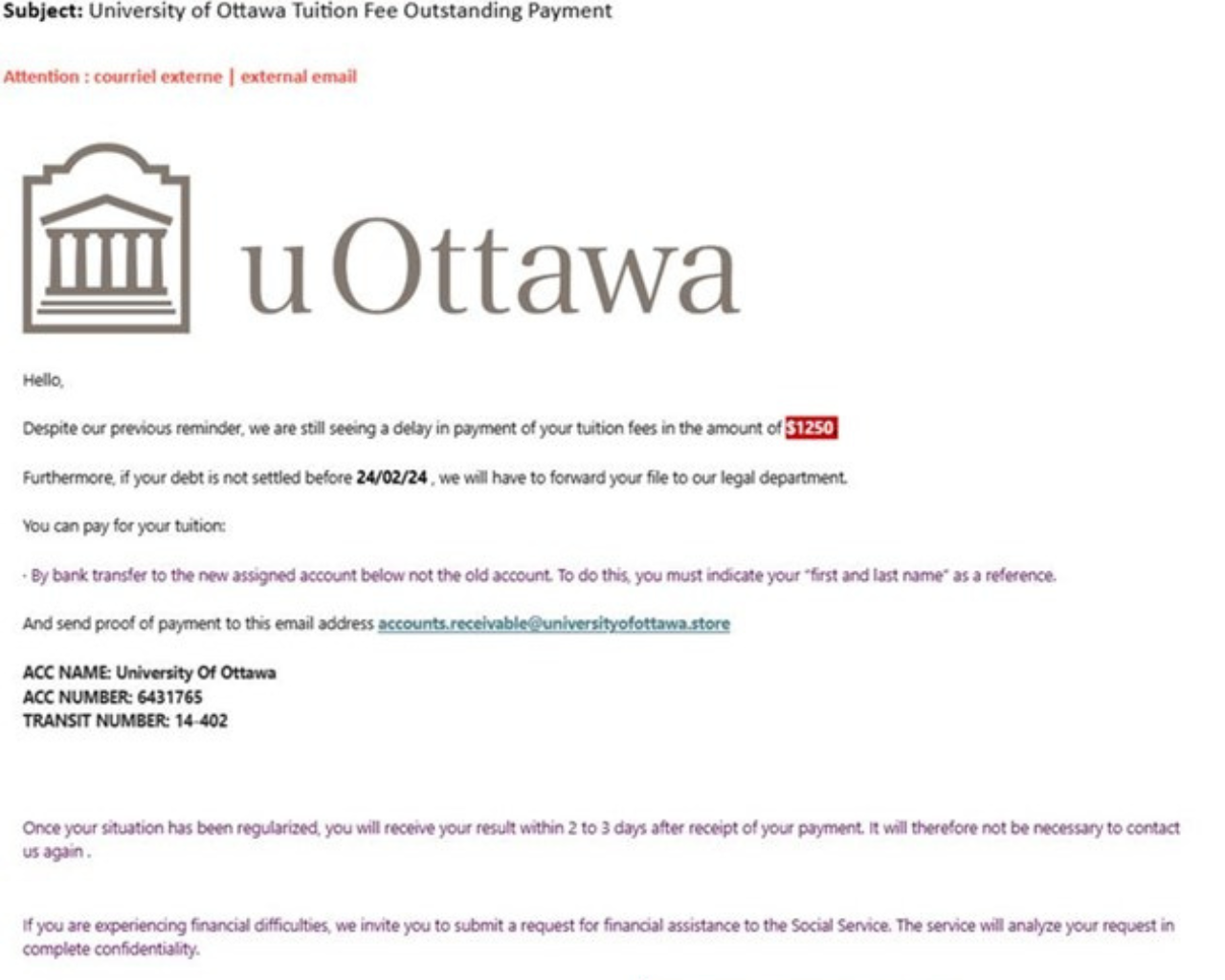
Outstanding tuition fee payment
Attackers impersonate university officials or departments to trick students into making payments for supposed outstanding tuition fees. These emails often contain urgent language and threaten legal action if the payment isn't made promptly. They typically ask for payment via bank transfer or other methods that are difficult to trace

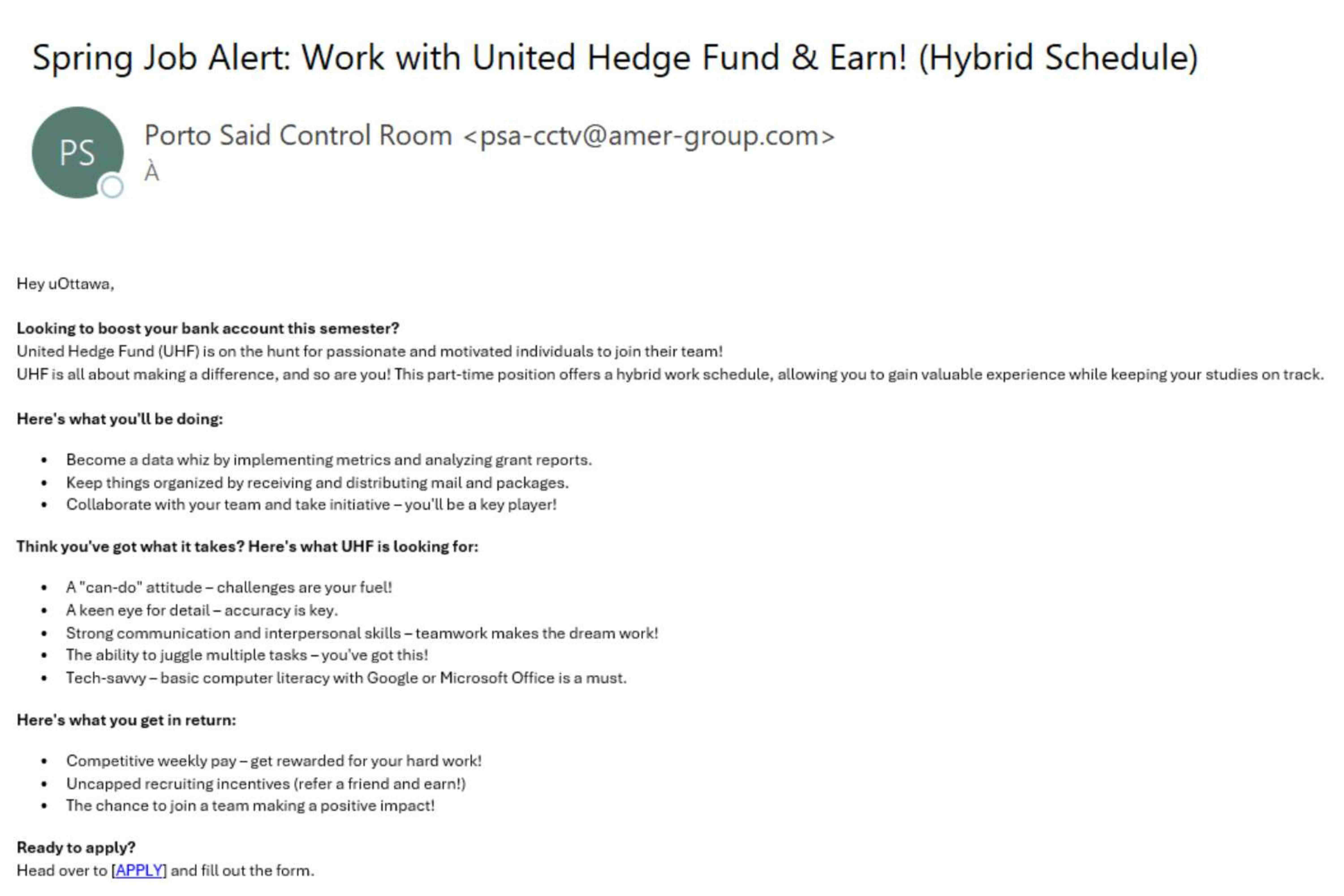
Fake job offers
Scammers pose as potential employers to trick people into providing personal information or money. These scams often exploit applicants’ eagerness to find employment through convincing language. They lure applications by using phrases like "automatically qualified" and "no interviews." They exploit job seekers by promising lucrative jobs or work-from-home opportunities.

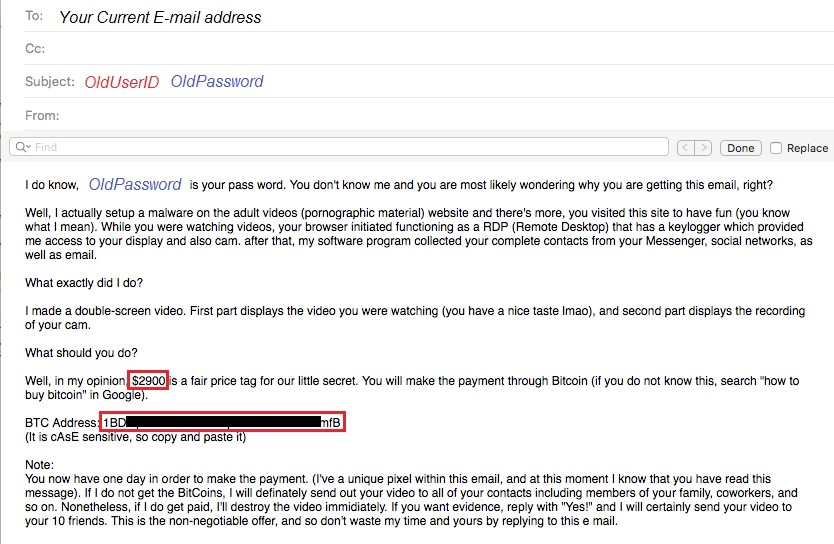
Sextortion scam
Scammers begin the email with a convincing personal detail like a current or former password and threats of leaking compromising images, videos and links to sites you have visited. Don’t panic, this is a “sextortion” scam email. It is very unlikely the hackers are in possession of compromising material. Your personal information was most likely obtained from lists of stolen or leaked passwords. A bulk message is sent to all users on that compromised list in the hope of extorting money from some users.
Take action
Sextortion and ransom emails
Here’s what you need to do:
- Never pay the ransoms.
- Do not click on any link and don’t open any attached file. Delete the email right away.
- Change your passwords for all your accounts.
- Install updates for all your software and antivirus.
- Enrol into Multi-factor authentication.
Tuition fee outstanding payment email
Here’s what you need to do:
- Take a moment to assess the situation calmly, scammers often use urgency to create panic
- Avoid replying to the email or clicking on any links. This could lead to further phishing attempts or malware
- Contact the University of Ottawa's financial office directly using official contact information found on the university's website or through your uoZone student portal.
- Do not use any contact details provided in the suspicious email
- Log into uoZone to verify your tuition balance. Legitimate institutions handle payments through secure methods.
- Use the Report Message function in Outlook to notify Information Technology. You can also contact the Service Desk for assistance.
- Regularly check your financial accounts and recent sign-in activity for any unauthorized access
Fake job offer email
Here’s what you need to do:
- Avoid replying to the email or clicking on any links.
- Contact the University of Ottawa's Career Development Centre or the company directly using official contact information if they are available. Do not use any contact details provided in the suspicious email
- Look for common signs of job scams, such as requests for upfront payments, guaranteed employment, vague job descriptions, poor grammar, unsolicited offers, high-pressure tactics, and requests for personal information
Prevent phishing and be alert
Given the potential damage phishing attacks can cause, we are reminding everyone to be diligent when dealing with unsolicited electronic communications, links and attachments.
Scams regularly circulate us and target the University. Be extra vigilant and exercise safe practices:
- Carefully check all links before clicking them. When in doubt, ask someone around you.
- Be suspicious of emails that require you to enter your account and password.
- Remember that malicious attempts may come from uOttawa addresses that have been compromised.
- Be extra cautious of job offers requiring you to provide your personal information.
- Question emails that mention your account, such as it being terminated, requiring you to log in to continue, etc. These are typically fraudulent. Exit the email and contact the Service Desk independently to verify the authenticity of the notice.
We encourage you to continue to report suspicious emails by using the Report Message function in Outlook.