Gazette
Stories and news from across campus.
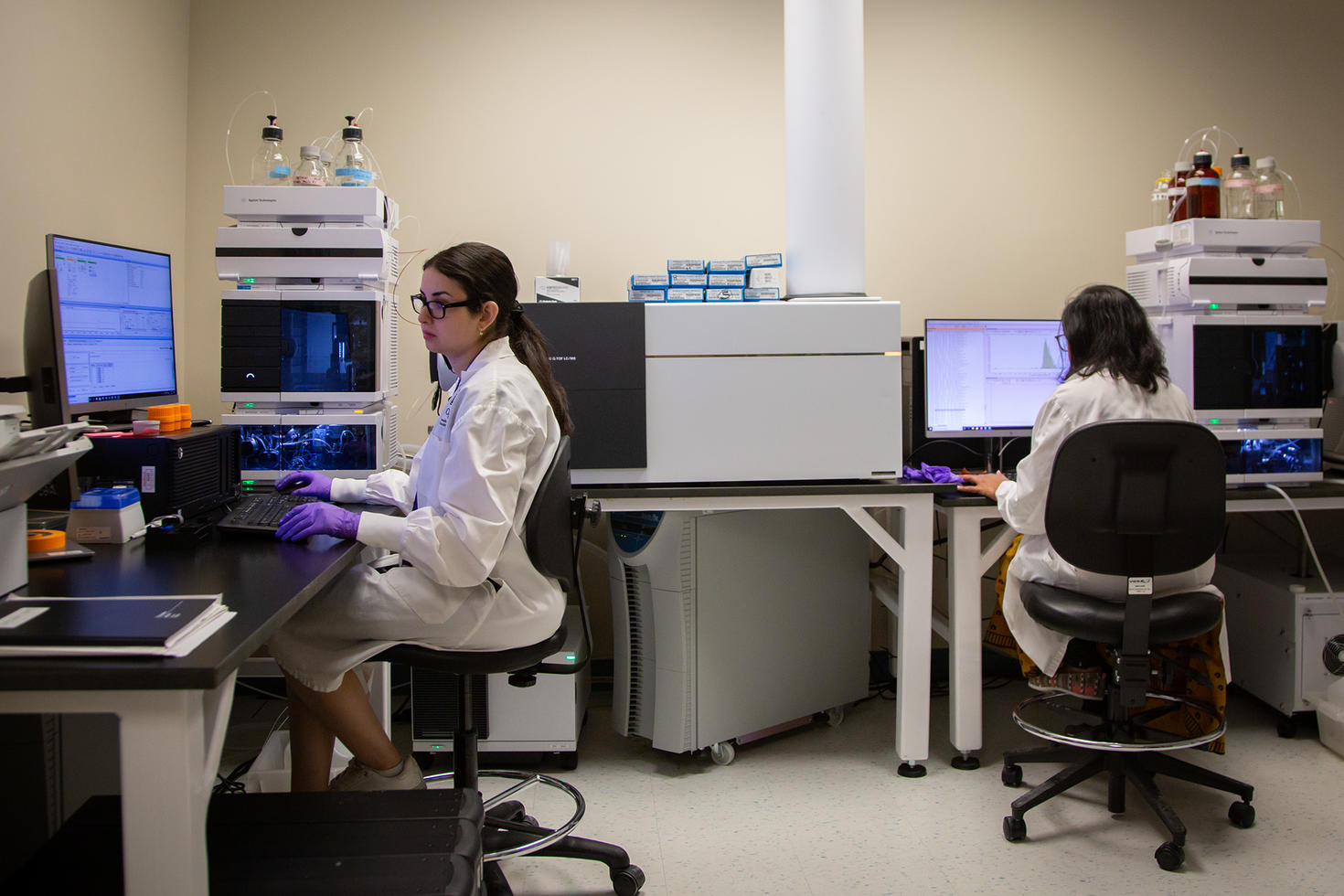
Ending the Drought: Ottawa’s Medical Research Community Welcomes Long-Awaited Wet Lab Facilities
Most people only think about their metabolism when their pants get too tight, blaming weight gain on their metabolism slowing down.
The University of Ottawa’s new Advanced Medical Research Centre will accelerate discovery and new treatments
The rapid development and deployment of vaccines during the COVID-19 pandemic highlighted the critical role of research in creating lifesaving medical…
If you build it, they will stay: Ending Ottawa’s biotech brain drain
Ottawa has earned its global reputation as a vibrant city for medical research and innovation. But if it wants to keep its intellectual capital in the…

Walking Toward a Better Future: How Smart Insoles and AI Are Revolutionizing Neurological Care
What if a pair of shoes could help detect disease progression before it shows? That’s the promise behind the collaboration between uOttawa researcher …

How eulachon grease links generations, culture and cutting-edge science
In the coastal First Nation communities of British Columbia, the return of a small, silvery fish each spring marks much more than a seasonal cycle. Fo…
The University of Ottawa and Canadian Nuclear Laboratories accelerate low dose radiation research and foster next generation of scientists
University of Ottawa (uOttawa), one of Canada’s most innovative universities and the Canadian Nuclear Laboratories (CNL), Canada’s premier nuclear sci…

Bridging innovation: uOttawa and Kinaxis forge a pathway between research and industry
In Ottawa’s tech corridor, where innovation pulses through labs and boardrooms alike, a new chapter is being written—one where academia and industry w…

Sociological Perspectives on Cultural and Religious Norms Influencing Child Marriage in South Sudan
Why does child marriage persist in parts of the world despite international efforts to end it? This is the complex question explored in a compelling n…

Transforming research through cognitive accessibility and neuroinclusive research
What if a simple form could shut someone out of research that could change their life?
For millions of neurodivergent individuals—those who identif…
For millions of neurodivergent individuals—those who identif…
Jun 27
to
Aug 7
Virtual orientation sessions for international students
We're hosting a variety of virtual orientation sessions for new international students. Get to know your Regional Mentor, have all your questions abou…
Jul 15
Fostering Sustainable Learning in Science and Environmental Education: Leveraging Low-Cost Educational Materials to Achieve SDG 4
The Faculty of Education is organizing an international symposium featuring guest speakers on July 15, 2025, and welcomes you to attend and engage in …

Professional Development Institute Events
The Professional Development Institute is proud to offer networking and educational events featuring national and international experts on current topics such as government, security and policy, leadership and more.
See all PDI upcoming events

uOttawa grows Kanata North’s presence to meet rising innovation demands
New campus space at 350 Legget anchors research, innovation, and talent where the industry needs it most.

Incoming president Marie-Eve Sylvestre sees a world of possibilities
Marie-Eve Sylvestre is preparing to begin a new chapter at the University of Ottawa, as president and vice-chancellor. Her enthusiasm is contagious. R…

A $2-million donation from Power Corporation of Canada will support student mobility and research to combat homelessness
Power Corporation of Canada will donate $2 million to the University of Ottawa to expand global learning opportunities for students and support urgent…

uOttawa media newsroom
Discover more stories, find an expert and explore uOttawa experts in the news.
Explore media
From isolation to a genuine sense of Indigenous belonging on campus
When Tiffany Angel Dunphy, a Wolastoqiyik from the Madawaska Maliseet First Nation, tried to imagine her life at the University of Ottawa, she foresaw…

Graduating with purpose: uOttawa students reflect on advocacy and hope
As the University of Ottawa celebrates the class of 2025, two graduates stand out for their commitment to gender and sexuality advocacy, blending acad…

20 courses you didn’t know you could take at uOttawa: 2025-2026
With courses ranging from cinema to witchcraft, there’s much to discover.
The University of Ottawa offers a broad range of prerequisite-free electi…
The University of Ottawa offers a broad range of prerequisite-free electi…


A look back on CCERBAL 2025 and Carrefour francophone
Two major events this spring featured several opportunities to quench your thirst for knowledge and to connect with peers.

Building the future of French-language education: A promising agreement between the universities of Regina and Ottawa
Over the years, too many young Saskatchewan francophones have seen their dreams of university studies in French come up against a tough choice: to lea…

Three OLBI professors get Learning Futures Fund support
OLBI is pleased to announce that projects by our professors Reza Farzi, Parvin Movassat and David Pratt will receive Faculty of Arts Learning Futures …

Partnership accelerating medical capacity in Tanzania
VR learning touted as a “new high” in knowledge sharing as uOttawa continues goal of improving medical care internationally.

Healing hearts: A new way to help the body recover after a heart attack
Biomedical engineering master’s student Jéssica Hernández Juárez researches materials that could improve life after heart attacks and help ease the bu…

The future of public health in Canada: How wastewater research continues to make a difference
With a new Genome Canada and NSERC Alliance grant for wastewater monitoring, Robert Delatolla and his team at the University of Ottawa Faculty of Engi…
Powering your phone with a laser
uOttawa researchers demonstrate new laser power converters to transmit power to further, remote destinations.

How a partnership with Fortinet is equipping computer science and engineering students for cybersecurity careers
The University of Ottawa’s Faculty of Engineering is bridging the gap between academic learning and real-world application through strategic industry …

Lessons from Montreal’s dismantled Champlain Bridge: Extending the life of Canadian infrastructure
New sustainable approaches could make our bridges safer and serviceable for longer. Civil engineering PhD candidate Issa Fowai is helping shape the fu…

The hidden costs of being a woman at work
As a renowned professor of psychology in the industrial-organizational program at Pennsylvania State University, Dr. Grandey took the stage at the Tel…

Entrepreneurial women: Olga Koppel’s quest for cleaner cities
“Pivoting is the one constant in starting a business.” That’s how Olga Koppel describes her journey from academia to entrepreneurship.

CEO Magazine ranks Telfer the #1 global executive MBA and a tier one MBA
Ottawa, ON – The Telfer School of Management proudly announces that its graduate programs have once again secured top recognition in the 2025 CEO Maga…

What a study about prison theatre reveals about rehabilitation
In a makeshift theatre inside a federal prison on Vancouver Island, incarcerated men adjust lights, paint backdrops and rehearse lines.

Theatrical innovation with sensory immersion as a creative force
Anne-Marie Ouellet, an associate professor in the Department of Theatre, is exploring an innovative approach to playwriting. Rather than starting from…

An all-women production of "The Wolves" takes centre stage at the University of Ottawa
The University of Ottawa Drama Guild brings together students from diverse backgrounds for a remarkable theatrical experience. This year, the Guild pr…

Spotlight on ageism in the workplace
As a long-ignored problem, ageism would rarely ever come up in conversations about workplace equity. But the tide is turning. Since the 2021 publicati…

Supporting vulnerable students and improving school attendance
Missing more school days is linked to poor long-term life outcomes, especially for those with disabilities and mental health challenges.

Sociological Perspectives on Cultural and Religious Norms Influencing Child Marriage in South Sudan
Why does child marriage persist in parts of the world despite international efforts to end it? This is the complex question explored in a compelling n…
Faculty news
Contact us
Gazette news
Tabaret Hall
550 Cumberland Street, room M284
Ottawa ON K1N 6N5
Canada
Tel: 613-562-5800 extension 5708
Fax: 613-562-5117
[email protected]
Submit your story
Have ideas for story? Want to get your initiative out there? Reach out to our team to submit your story at [email protected].

